Govern, Secure, and Monitor Enterprise AI
Your Control Plane for Secure Enterprise AI
A unified platform to govern, secure, and test enterprise AI across every application, agent, and interaction

Govern, Secure, and Monitor Enterprise AI
Your Control Plane for Secure Enterprise AI
A unified platform to govern, secure, and test enterprise AI across every application, agent, and interaction
Introducing Velyana
Introducing Velyana
Velyana is an AI governance and security control plane that sits between your AI applications, agents, and large language models — enforcing policies, preventing data leakage, and providing full visibility into AI usage
Velyana is an AI governance and security control plane that sits between your AI applications, agents, and large language models — enforcing policies, preventing data leakage, and providing full visibility into AI usage
Velyana is an AI governance and security control plane that sits between your AI applications, agents, and large language models — enforcing policies, preventing data leakage, and providing full visibility into AI usage
AI Runtime Security
AI Runtime Security
AI Red Team
AI Red Team
Shadow AI
Shadow AI
AI Governance
AI Governance
AI Agent Security
AI Agent Security
AI Runtime Security
AI Red Team
Shadow AI
AI Governance
AI Agent Security

The Architecture of Certainty
The Architecture of Certainty
One platform, four modules
Securing AI from Discovery to Defense
One platform, four modules
Securing AI from Discovery to Defense
Four mission-critical modules designed to identify, mitigate and neutralize threats in high-velocity AI environments.
Four mission-critical modules designed to identify, mitigate and neutralize threats in high-velocity AI environments.
Forge Attack
Forge Attack
Red-team your LLMs at scale. Automated prompt injection testing and jailbreak simulations to find vulnerabilities before they are exploited.
Red-team your LLMs at scale. Automated prompt injection testing and jailbreak simulations to find vulnerabilities before they are exploited.
Explore AI Red Team
Explore AI Red Team
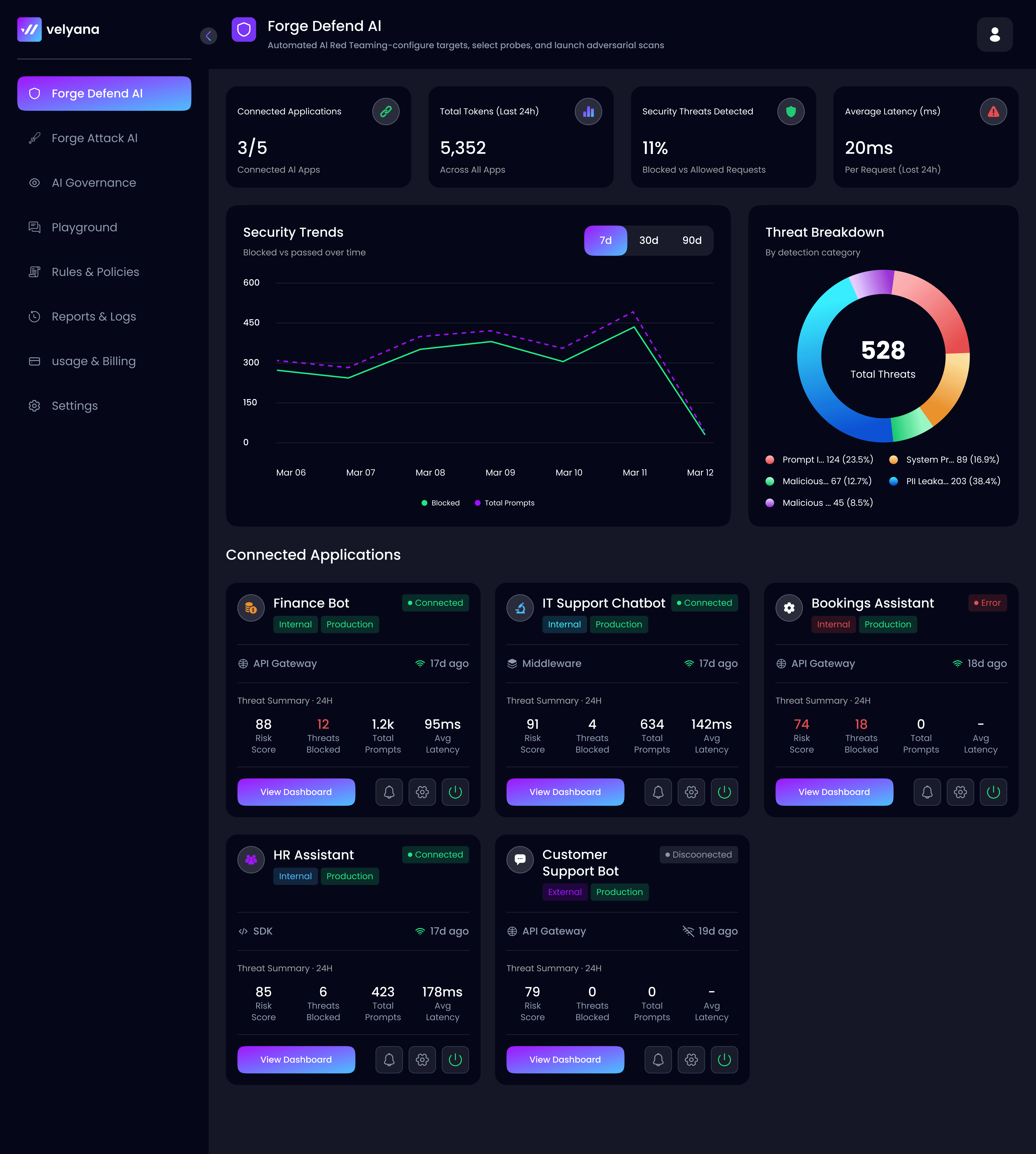
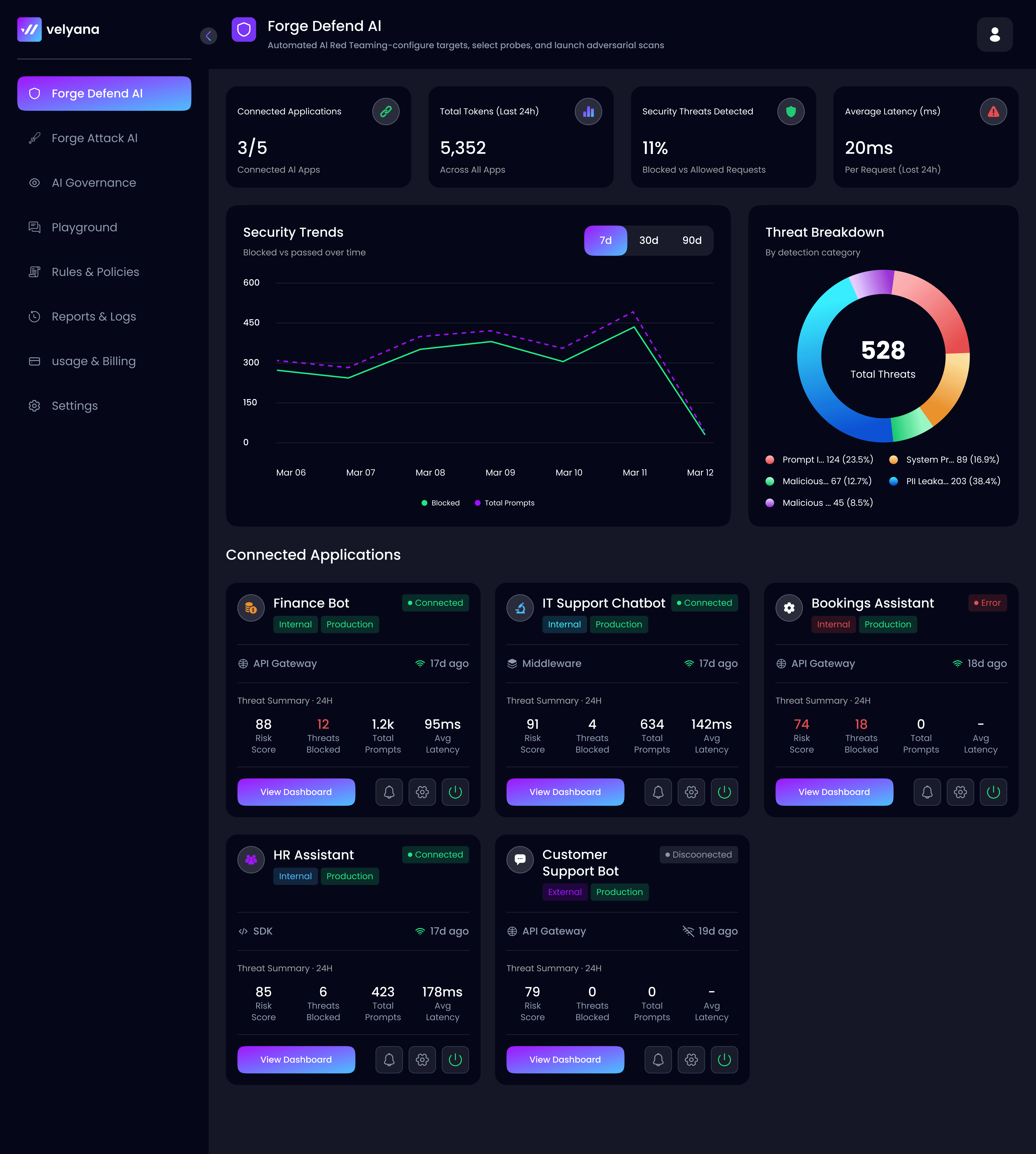
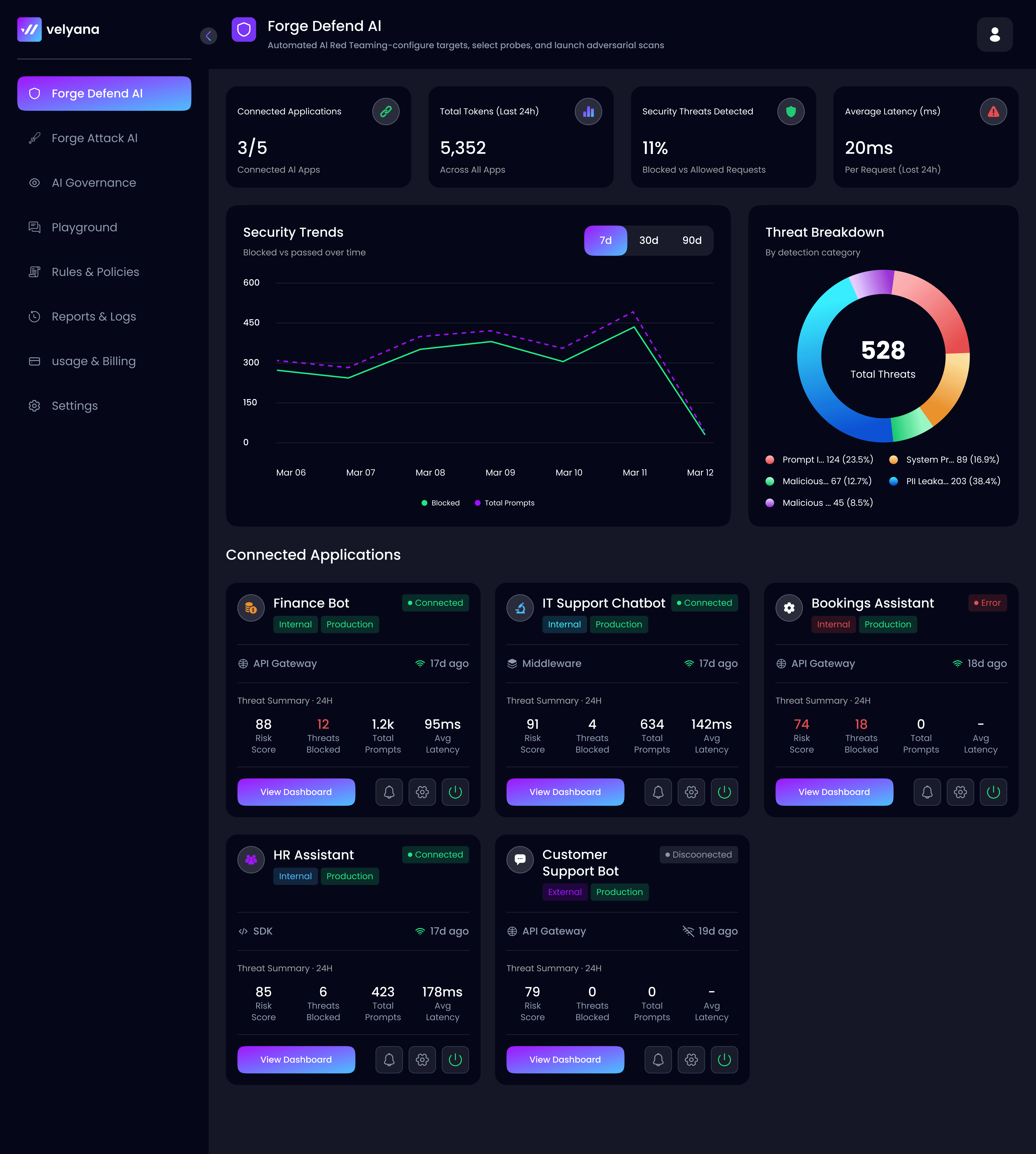
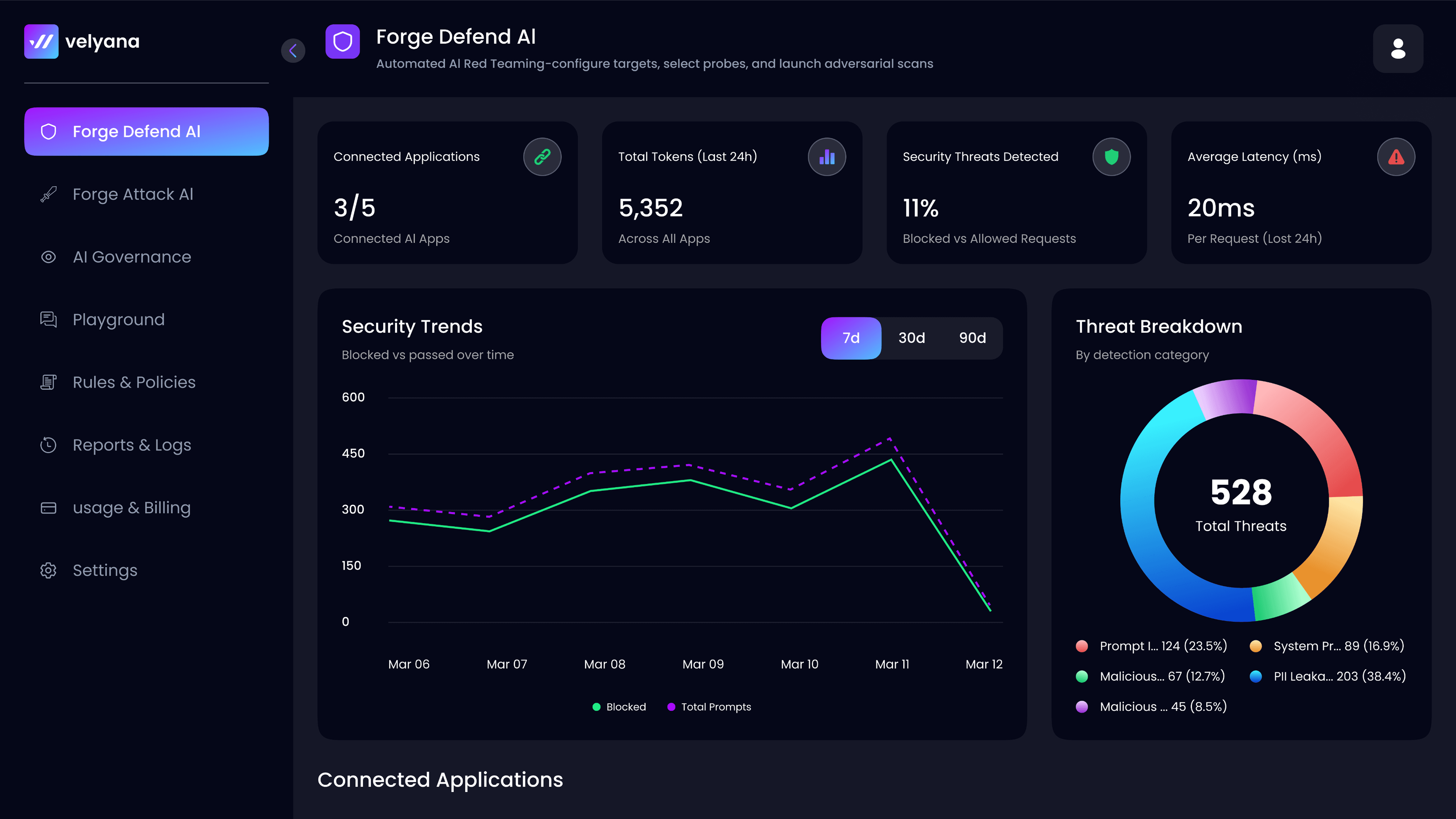
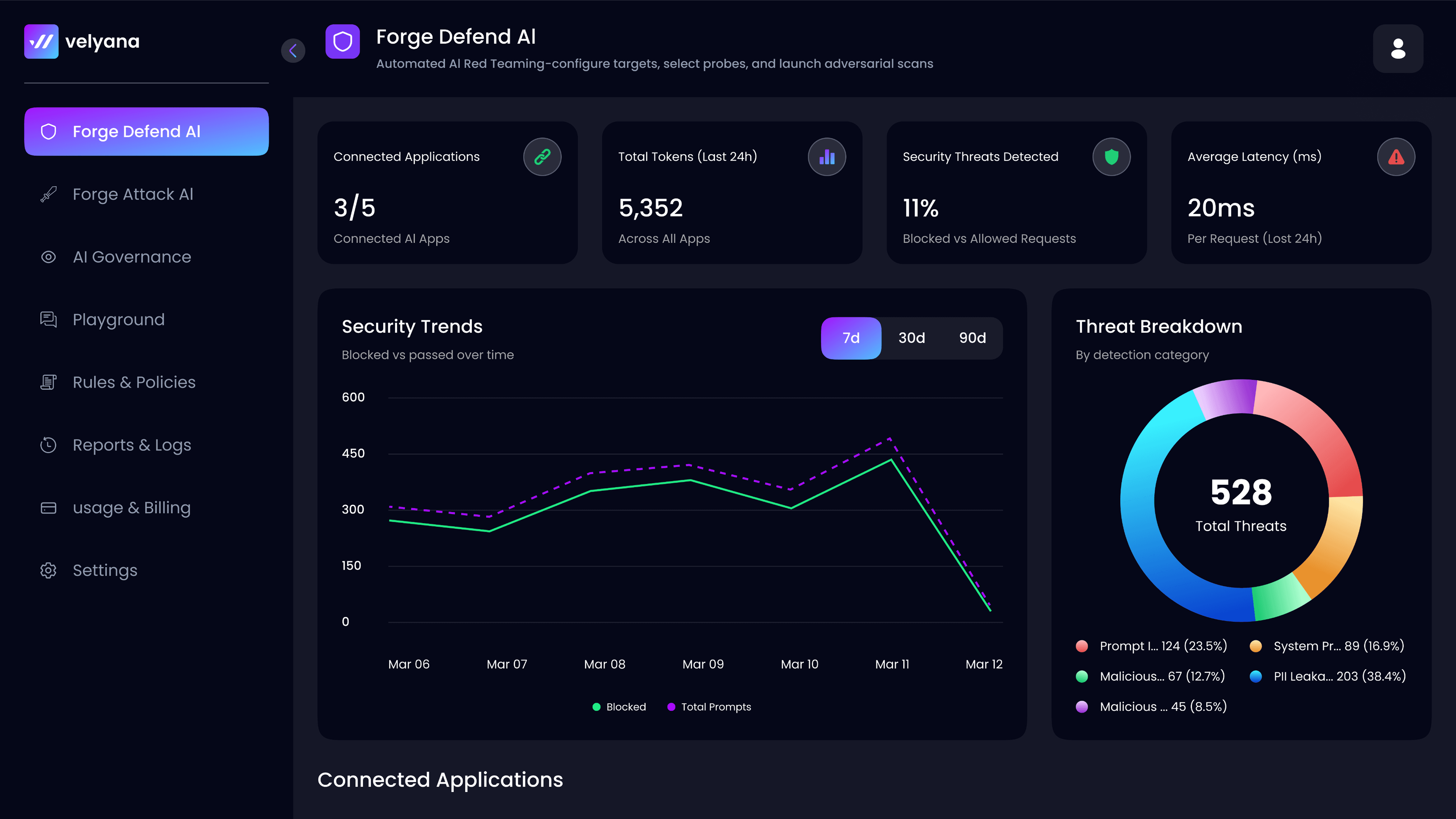
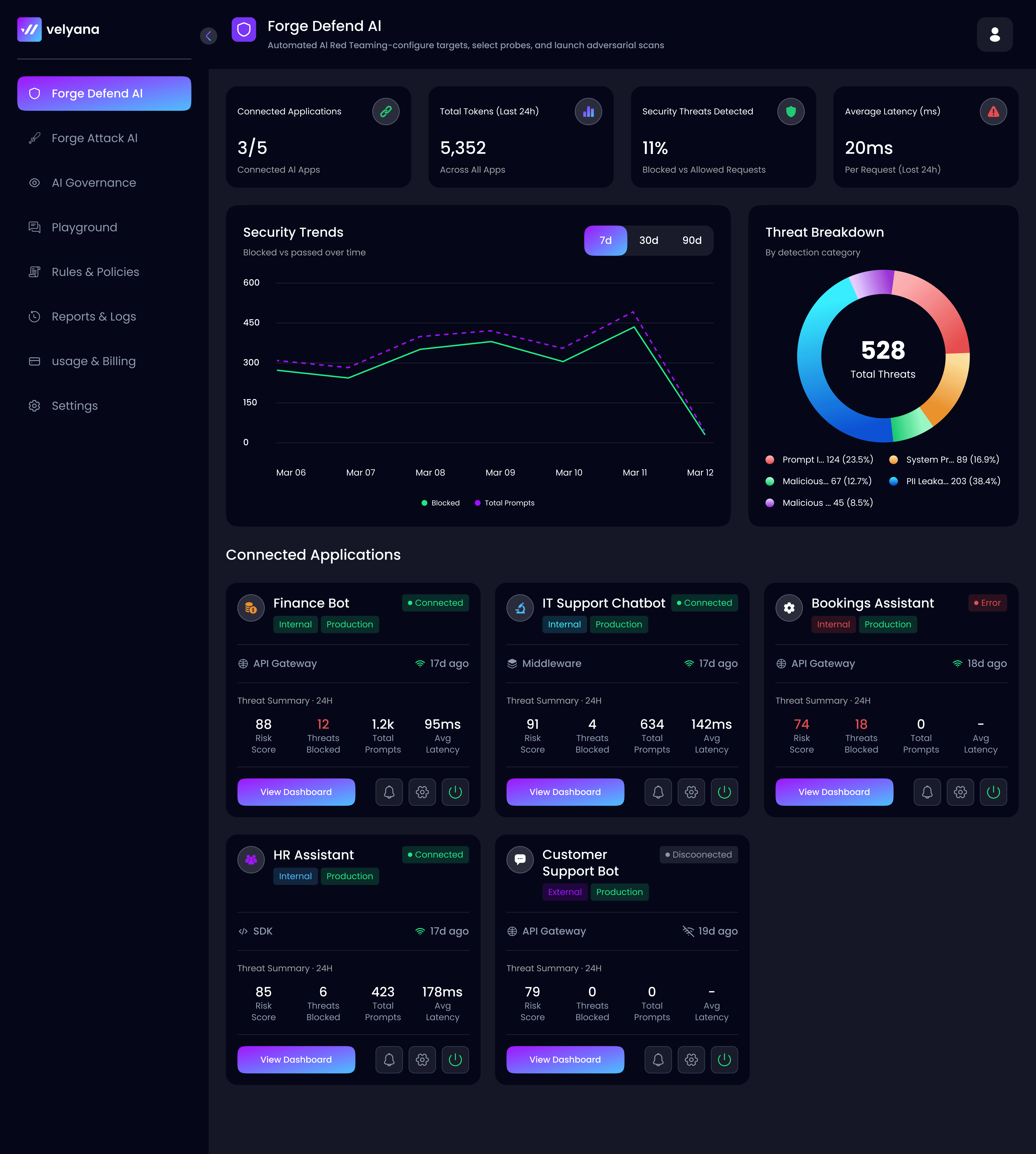
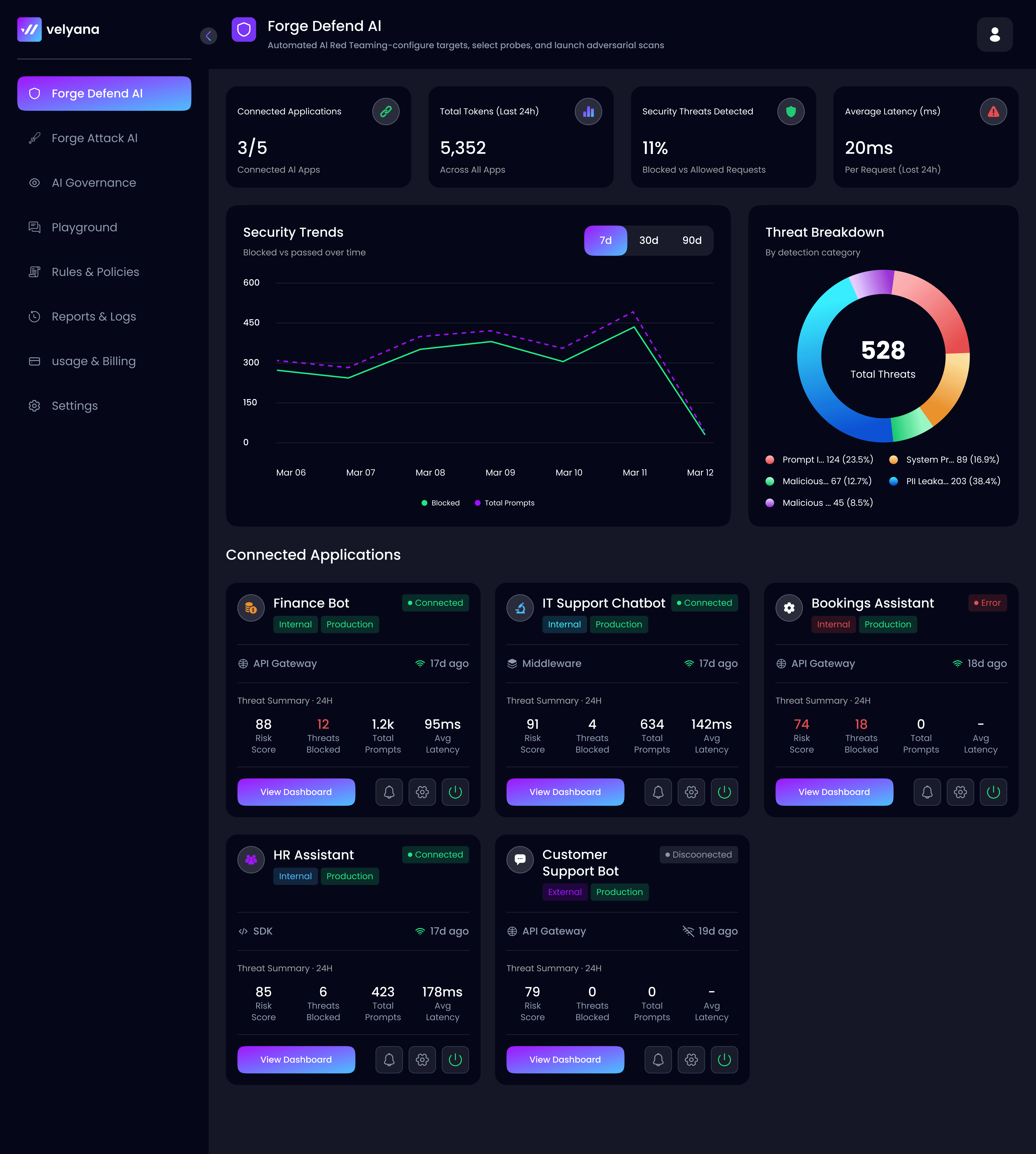
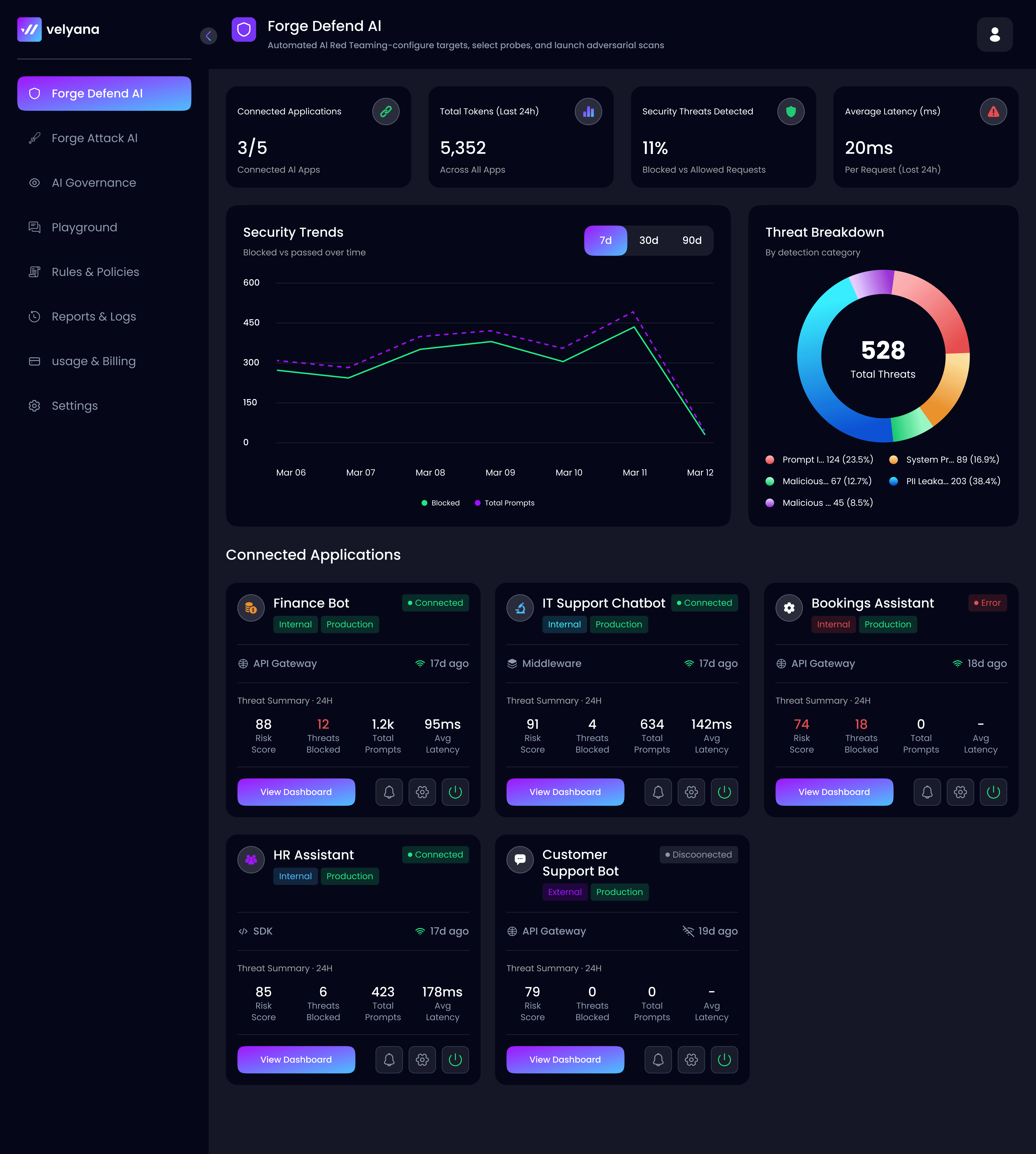
Forge Defend
Forge Defend
Real-time guardrails for every prompt and response. Zero-latency filtering for PII, toxic content, and adversarial signals.
Real-time guardrails for every prompt and response. Zero-latency filtering for PII, toxic content, and adversarial signals.
Real-time guardrails for every prompt and response. Zero-latency filtering for PII, toxic content, and adversarial signals.
Explore AI Runtime Security
Explore AI Runtime Security
Shadow Al
Shadow Al
Full visibility into unauthorized Al usage. Map the data egress routes across your enterprise ecosystem instantly.
Full visibility into unauthorized Al usage. Map the data egress routes across your enterprise ecosystem instantly.
Full visibility into unauthorized Al usage. Map the data egress routes across your enterprise ecosystem instantly.
Detect Shadow Al
Detect Shadow Al
Al Agent Security
Al Agent Security
The world's first comprehensive security platform for autonomous agents. Control what your agents can see, do, and access with granular permission frameworks.
The world's first comprehensive security platform for autonomous agents. Control what your agents can see, do, and access with granular permission frameworks.
Agent Security
Agent Security

Security Coverage
Security Coverage
Comprehensive OWASP LLM Top 10 Coverage
Comprehensive OWASP LLM Top 10 Coverage
Forge Defend provides runtime protection for 6 of 10 OWASP categories. Forge Attack can test for 9 of 10 pre-deployment. Together, the platform delivers the most comprehensive LLM security coverage available.
Forge Defend provides runtime protection for 6 of 10 OWASP categories. Forge Attack can test for 9 of 10 pre-deployment. Together, the platform delivers the most comprehensive LLM security coverage available.
#
Vulnerability
Forge Defend
Forge Attack
LLM01
Prompt Injection
LLM02
Sensitive Information Disclosure
LLM03
Supply Chain Vulnerabilities
-
LLM04
Data and Model Poisoning
-
LLM05
Improper Output Handling
LLM06
Excessive Agency
LLM07
System Prompt Leakage
LLM08
Vector and Embedding Weaknesses
-
LLM09
Misinformation
LLM10
Unbounded Consumption
-
#
Vulnerability
Forge Defend
Forge Attack
LLM01
Prompt Injection
LLM02
Sensitive Information Disclosure
LLM03
Supply Chain Vulnerabilities
-
LLM04
Data and Model Poisoning
-
LLM05
Improper Output Handling
LLM06
Excessive Agency
LLM07
System Prompt Leakage
LLM08
Vector and Embedding Weaknesses
-
LLM09
Misinformation
LLM10
Unbounded Consumption
-
Impact
Impact
Measurable security impact from day one.
Measurable security impact
from day one.
90%
90%
90%
Reduction in undetected AI vulnerabilities
99.2%
99.2%
99.2%
Threat classification accuracy
90%
90%
90%
Reduction in unauthorized AI data sharing
< 1 hr
< 1 hr
< 1 hr
Time to deploy Forge Defend
$7M+
$7M+
$7M+
Estimated annual savings from prevented breaches

Ready to Secure Your Enterprise AI Infrastructure?
Ready to Secure Your Enterprise AI Infrastructure?
Let us show you how we can help secure & govern your enterprise AI infrastructure - all the way from discovering shadow AI to securing complex AI agents.
Let us show you how we can help secure & govern your enterprise AI infrastructure - all the way from discovering shadow AI to securing complex AI agents.




Ready to Secure Your Enterprise AI Infrastructure?
Let us show you how we can help secure & govern your enterprise AI infrastructure - all the way from discovering shadow AI to securing complex AI agents.